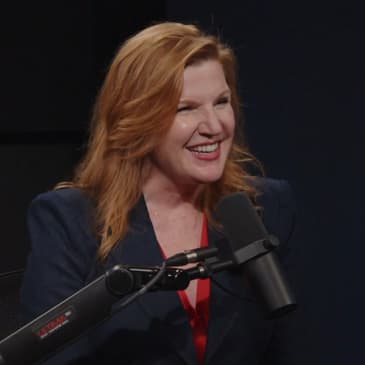
In this episode, Jenny Beth Martin speaks with Kirsten Davies, a cybersecurity expert and former Chief Information Security Officer for Fortune 500 companies. Kirsten shares insights into the critical need for cybersecurity education for everyday citizens, especially around election security and digital safety. She discusses her work at the Institute for Cyber Civics, a nonprofit she founded to provide practical, accessible guidance on cyber threats for both voters and election officials. The conversation also covers her passion for protecting youth from online dangers and how her organization aims to create a safer digital space for everyone.
Twitter/X: @Institute4Cyber | @jennybeth
Website: instituteforcybercivics.org
[00:00:00] Our youth of today are being targeted. They're being targeted online. They don't realize that everyone who presents themselves online isn't necessarily who they say they are.
[00:00:11] Keeping Our Republic is on the line, and it requires patriots with great passion, dedication, and eternal vigilance to preserve our freedoms. Jenny Beth Martin is the co-founder of Tea Party Patriots.
[00:00:24] She is an author, a filmmaker, and one of Time Magazine's most influential people in the world.
[00:00:30] But the title she is most proud of is mom to her boy-girl twins.
[00:00:35] She has been at the forefront, fighting to protect America's core principles for more than a decade.
[00:00:41] Welcome to The Jenny Beth Show.
[00:00:44] In today's episode, I'm joined by Kirsten Davies, a seasoned cybersecurity leader who has held top security roles at multiple Fortune 500 companies.
[00:00:54] Now, as the founder of the Institute for Cyber Civics, Kirsten is on a mission to empower everyday Americans with the tools and knowledge to navigate our digital world safely.
[00:01:05] We'll discuss election security, cyber threats, and how her new institute is working to protect our most vulnerable citizens from online risks.
[00:01:15] Kirsten, thank you so much for joining me today.
[00:01:17] Oh, such a pleasure. Thanks for having me, Jenny Beth.
[00:01:19] So, you have a brand new nonprofit. Tell me about this new nonprofit.
[00:01:23] I do. We're super excited about it.
[00:01:25] What we saw was a need for average everyday citizens to have cybersecurity guidance in things like banking and email and all the things that we do now in the digital universe.
[00:01:35] And what we've kicked off with is an inaugural effort around the cybersecurity of elections.
[00:01:41] So, voters, when we show up to the polls and election observers and election workers, we realized there was no practical guidance for people to be able to know what to look for when it came to cybersecurity.
[00:01:53] So, that's where we started off.
[00:01:55] That is really interesting.
[00:01:57] So, I think a lot of people around the country are more attuned to potential problems with cyber, maybe not necessarily cybersecurity, but just problems with computers because of the CrowdStrike disaster that happened this past summer.
[00:02:12] Yeah, the outage pretty much got everybody's attention, didn't it?
[00:02:16] It did. And that wound up being just, it wasn't a cybersecurity attack, but it was an upgrade that went bad, right?
[00:02:25] Yeah, it was an update on a particular folder. And the interesting thing around that is it did get everyone's attention. Why? Because laptops stopped working.
[00:02:36] You know, people who were trying to fly that day couldn't get on certain flights. You, well, you were impacted by that.
[00:02:42] You know, my cousin was supposed to come visit me that weekend and she actually called me the night that it happened and she said, they're giving me a paper ticket for my bag. Is this normal?
[00:02:53] And I was like, no, no. And I started looking into it and that was how I actually even found out about it.
[00:02:59] So these are the things that are getting average, everyday people's attention now.
[00:03:04] When you can't traverse the digital sphere the way that you expect to, it's supposed to be seamless.
[00:03:10] You're supposed to be able to get on a flight. You're supposed to be able to rent a car, check in and out of a hotel.
[00:03:15] When these things start to be impacted, boy, does it ever get people's attention.
[00:03:19] It does. So now with what you're doing with poll watchers and poll workers, what is that exactly?
[00:03:26] Yeah, absolutely. Well, we started looking around to see what guidance was out there for cybersecurity for the elections.
[00:03:32] Of course, there's guidance out there. CISA, the Cybersecurity and Infrastructure Security Agency under DHS, has issued guidance around election security.
[00:03:42] The Election Action Committee has done so. There's guidance out there.
[00:03:45] But what we noticed was it wasn't practical.
[00:03:49] Like it didn't, first of all, the language is very technical, which not a lot of people understand that.
[00:03:54] People in my industry do in cybersecurity.
[00:03:56] But average everyday people don't know what to do with that.
[00:03:59] And so as we were looking into it and trying to figure out, well, how would people know that there's a cyber incident underway?
[00:04:06] An election worker or an election official, for example, how did they know that there was a crowd strike issue?
[00:04:13] Well, there was what we call a blue screen of death that happened on certain machines, on certain laptops.
[00:04:19] And by then, you're kind of going, oh, what do I do about this?
[00:04:24] So when we were looking into election security and we're seeing that there's guidance out there around watch out for phishing, watch out for ransomware, watch out for DDoS.
[00:04:35] Well, what does that even look like?
[00:04:36] I mean, do you know what that looks like?
[00:04:38] I don't think people do.
[00:04:40] People in the cyber industry know what that looks like.
[00:04:42] So what we really wanted to do was create handbooks in average language, regular English language, to say, hey, if you see a blue screen of death, what could that mean?
[00:04:55] It's not a definitive prognosis of what the situation is, but it's understanding what symptoms to look for and then how to alert on that, like report it.
[00:05:06] Is it something that's unusual or abnormal?
[00:05:08] Yes, report that because it could be something.
[00:05:11] It doesn't mean that it is, but it could be something.
[00:05:14] I think that's really important.
[00:05:16] And I want to go into it, but we're going to come back to that.
[00:05:19] Hang on just a second.
[00:05:20] I know your background, but let's explain to people what your background is.
[00:05:24] Why should anyone listen to you?
[00:05:28] That's because my mom likes me very much.
[00:05:31] She should.
[00:05:32] She should.
[00:05:33] Yeah, look, I've been really blessed with an amazing career.
[00:05:37] I am a three-time chief information security officer.
[00:05:41] What does that mean?
[00:05:42] It means I was the executive in charge of cybersecurity for Fortune 500 companies.
[00:05:47] And before that, I was a two-time deputy chief information security officer for two more Fortune 500 companies.
[00:05:55] Some of them are on the global 200 list or the Fitzy out of London, that kind of thing.
[00:06:00] But I've been working on this.
[00:06:03] I've led teams.
[00:06:04] I've had the privilege and the pleasure to lead teams, globally speaking, trying to be very effective at reducing cybersecurity risk for Fortune 500 companies.
[00:06:16] And so across the teamwork that we've done, I've also worked with other global CISOs, as we're called, or CISOs if you're in the government sector.
[00:06:25] I've worked with other global CISOs who have done exactly what I've done also at other organizations.
[00:06:30] I put together a tech advisory council of some of these amazing and brilliant CISOs as well.
[00:06:35] And one of the primary things that we do in cybersecurity is to build awareness through the employee base of, hey, if you see something, be aware.
[00:06:47] Don't click the links, right?
[00:06:48] You might have, for your viewers who work for major corporations or even small companies, you may see this guidance.
[00:06:55] You know, don't click those links that come in through emails.
[00:06:57] Be suspicious of text messages that you get.
[00:07:00] So these are some of the primary things that we've done across these major organizations.
[00:07:04] And I thought, well, a lot of small-sized businesses and average everyday citizens don't get that guidance unless they're working for a big corporate that does this kind of a thing.
[00:07:17] So I really wanted to bring that experience and that knowledge and that wisdom that I've been blessed with into folks' homes.
[00:07:26] You know, teaching my dad how not to click on links.
[00:07:30] You know, there isn't that guidance that's out there, and that's what I really wanted to accomplish by establishing this institute.
[00:07:35] I think that it is so important.
[00:07:37] And I can think of a thousand different ways that it could be useful beyond even beyond elections.
[00:07:43] And I'm sure you've thought of 10,000 different ways it could be useful.
[00:07:46] Just need more time.
[00:07:47] Yeah.
[00:07:49] So I used to program computers, and I worked for Fortune 500 companies as well.
[00:07:55] And one of the things that I have found very interesting when I was looking at problems and potential problems and reports of issues that may or may not have been problems from the 2020 election is that,
[00:08:11] and then talking to attorneys who've worked on election integrity, they don't understand computer systems.
[00:08:19] They don't understand the testing process, the Q&A process, what would actually ever be allowed in a Fortune 500 company to happen at all.
[00:08:32] And I'm just surprised by that because I look at things and I'm like, you know, I worked at the Home Depot and program computers at the Home Depot when they were a Fortune 10 company.
[00:08:45] They may have been a Fortune 5 company.
[00:08:46] So this is the everything.
[00:08:50] Everything, and I did not work on the computer systems that were inside the stores, but everything that was drilled into us the entire time I was working there is never do anything that will bring the computer systems down in the stores ever.
[00:09:04] Because every minute that it's down or every hour that it's costing the store money.
[00:09:09] That's right.
[00:09:09] It's costing the company money.
[00:09:10] That's right.
[00:09:11] And before that, I worked at the Mead Corporation, which I worked in a computer, I worked in a paper mill and supported computer systems in a paper mill.
[00:09:20] And the goal there was never to cause a paper machine to go down because if the paper machine goes down and it's not making paper, you're not making money.
[00:09:28] That's right.
[00:09:28] These are simple things that you think about with everything, then everything you do, you go, okay, if what I'm doing, is it going to cause the machine to go down or is it going to cause the stores to go down or not have what they need?
[00:09:43] And then you work backwards.
[00:09:44] How can I avoid that?
[00:09:45] Can I do it at a certain time?
[00:09:48] When I worked at the Home Depot, there would be updates on weekends, holiday weekends when the store would be closed.
[00:09:56] That's right.
[00:09:56] Because the store is closed.
[00:09:57] That's right.
[00:09:57] So that isn't great for the families of the people who are in the computers, but it's just sort of the way that it worked.
[00:10:09] When I looked at what happened with the elections, some of the updates that were happening, I just was sitting there going, wait, you're allowing an update to happen on a server that supports, I noticed this in 2022,
[00:10:22] that supports the entire poll pad system or the check-in system for checking in to vote.
[00:10:33] And it was like, oh, it's just a routine update.
[00:10:44] And I'm sure there are conspiracy theorists who would say, or people who've investigated it all, oh, it was actually a deliberate attack.
[00:10:54] But based on what I learned, I don't think it was a deliberate attack.
[00:10:57] I just think they thought, oh, we can just go ahead and do this routine update that we would normally do, and it won't be a problem.
[00:11:04] But it is a problem in the middle of voting.
[00:11:06] That's right.
[00:11:06] And it's a problem in any arena.
[00:11:09] So when you think about it, in terms of what you've mentioned around voting, when we talk about a go-live window, which you would be very familiar with in technology,
[00:11:18] that's when you have a software application that's been developed and tested and checked out every which way to Sunday,
[00:11:27] and then it goes out of the development environment into a testing environment where it's tested out to make sure it interacts well with an operating system,
[00:11:37] like all of these layers of technology that it has to interact really well with.
[00:11:42] By the way, sidebar, the update on the CrowdStrike was not appropriately tested for how it would interact with the Microsoft operating system.
[00:11:51] So that's what I'm talking about there, which I know you're super familiar with.
[00:11:54] But back to the topic here.
[00:11:56] After it's all tested out, then it goes into what we call prod production.
[00:12:01] That's when it's live for everyone to use, whatever the audience is, the user audience that we talk about.
[00:12:07] Once it's live in that production environment, any changes, any updates, any version upgrades of anything affiliated with that particular piece of software
[00:12:18] have to go back through the cycle of development of any code that's there and go through the gates to have it checked,
[00:12:26] go into test, have it checked out and test before you can update it back into prod, right?
[00:12:32] Into production.
[00:12:34] And the challenge that we see when anything that goes through, that's teed up to go through into production,
[00:12:42] if it doesn't have all of that testing, how do you know what's going to happen?
[00:12:46] You don't know what's going to happen.
[00:12:47] And so for mission-critical software, which I would argue some of the software where we have the voter databases,
[00:12:58] the registration aspect of it, the accumulation of the votes themselves, and then the tabulation of those votes.
[00:13:06] Especially during voting.
[00:13:08] During voting.
[00:13:09] Not when you're not voting, but during voting.
[00:13:13] During voting is what we would consider to be a change freeze window.
[00:13:17] That's what we call an IT.
[00:13:18] An IT change freeze window is you do not make any changes to any part of the stack that supports that critical process
[00:13:29] without going through some serious, serious rigor.
[00:13:33] Testing, four eyes principle, you've got several people watching, you do a ton of testing.
[00:13:38] And I would argue, and one of the things that we put in the handbook for election officials is during voting,
[00:13:49] that is a change freeze window.
[00:13:52] Period.
[00:13:53] Right.
[00:13:53] Period.
[00:13:54] We would argue that's best practices in cybersecurity.
[00:13:57] On any of the computer systems.
[00:14:02] That's right.
[00:14:02] We're not talking about the ones that are named in the news.
[00:14:05] And I think this was just a server, and under normal circumstances, you could update the server once a week,
[00:14:12] and it's not a big deal.
[00:14:14] But in the middle of voting, it may not be a big deal.
[00:14:18] It could be, though.
[00:14:19] But it could be.
[00:14:20] Because think about what happened with CrowdStrike.
[00:14:22] And they did that update, and it just shut down things globally.
[00:14:27] Blue screen of death.
[00:14:28] So we just don't know.
[00:14:30] And so when we're thinking about such a small window for voting and for elections, that is a very small window that we at the Institute would argue.
[00:14:39] That is a change freeze window.
[00:14:41] Nothing gets updated.
[00:14:42] There's no maintenance.
[00:14:43] There's no version upgrades.
[00:14:45] There's no software patches that are released.
[00:14:47] And what we would argue that's good practices is if there is something where there's a perception of something going wrong or something that is abnormal, we'll call it abnormal, with the behavior of a server or of a voting machine or a software, whatever that is, take it out of commission.
[00:15:07] Stop using it.
[00:15:35] It's a server upgrade.
[00:15:36] A patch that happens that hasn't been completely and fully tested through the entire life cycle of the process of that.
[00:15:46] You can't guarantee that there's integrity in the outcome of it.
[00:15:50] It's pretty simple.
[00:15:52] It is.
[00:15:53] It's very techie, though, right?
[00:15:54] And I try to be quite educational and more understandable language than what we talk about in techie, right?
[00:16:04] We can kind of go off and be really geeky and techie.
[00:16:06] But the point is that this isn't mysterious to technologists like you and me.
[00:16:12] There's no mystery or black box involved in these kinds of things.
[00:16:15] And so the public really should be demanding that they can understand what's going on, that there's transparency involved in this, and that there's integrity in the process, and that we're following best practice principles in IT and cybersecurity.
[00:16:31] Okay, so now let's take it back to what you've got for poll watchers and poll workers.
[00:16:38] You've got two different handbooks?
[00:16:40] That's right.
[00:16:40] That's right.
[00:16:41] Describe what's in this.
[00:16:42] Yeah.
[00:16:43] First of all, it's voluntary.
[00:16:43] So we know in many states across the United States there's quite a process for being involved in the election training, whether that's for the election officials or the poll workers themselves who are hired and paid,
[00:16:57] and also the training that's available for the poll watchers or the election observers.
[00:17:02] So what we've done is we've created handbooks that are based upon cybersecurity good practices that we know about in Fortune 500, Fortune 50, Fortune 5, as the case may be.
[00:17:15] And we've boiled it down into particular potential issues.
[00:17:23] These are guided based upon what we understand from threat intelligence of what could go wrong because it's technology,
[00:17:29] what could go wrong because it's the digital universe.
[00:17:32] And we've boiled it down into potential cybersecurity issues.
[00:17:37] We've given really common language and its symptomatic description for the officials, the workers, or the observers to be able to read the example and go,
[00:17:51] Oh, okay, if I see this, then it might be a potential that, and hey, I need to pay attention to that.
[00:18:00] So for example, if you wanted to look at a change freeze, for example, if an individual, and this is in both of the handbooks,
[00:18:09] if an individual comes in, it could be an IT service provider, it could be somebody with an official looking badge,
[00:18:17] it could be a member of the poll working team themselves.
[00:18:21] If someone comes in during early voting or on election day itself and says,
[00:18:27] I need to update those machines,
[00:18:30] one of the potential issues is, hang on,
[00:18:33] we should be considering this a change freeze window, which we talked about,
[00:18:37] and the officials and the observers both should have a conversation about this.
[00:18:45] So that's a potential issue that we've highlighted in both of the handbooks to say,
[00:18:50] this is not cybersecurity best practices to do a service maintenance,
[00:18:56] to do a patch, to do a version upgrade,
[00:18:59] any of those things that that individual could be saying,
[00:19:03] Hey, I need to do this right now.
[00:19:04] We'll push back on that.
[00:19:05] Wait, raise your hand and say something.
[00:19:08] And then you report it and see where it goes.
[00:19:12] That's right.
[00:19:13] And it may not be anything.
[00:19:14] Like the Secretary of State may know that this is actually something that needs to happen for whatever reason,
[00:19:19] but don't do it blindly.
[00:19:21] Absolutely.
[00:19:22] And that's the whole point.
[00:19:23] It kind of goes back to that really great campaign.
[00:19:27] And I think it was Amtrak a long time ago that said,
[00:19:30] see something, say something.
[00:19:31] It's the same thing in the digital universe.
[00:19:33] For example, if your phone starts going off with SMS text messages with click here, click here, this is urgent, this is urgent, click here, click here.
[00:19:43] We should be suspicious of those things.
[00:19:46] Why?
[00:19:47] Because threatsters, threat actors themselves.
[00:19:51] We know, for example, there was a recent breach of millions of people's login credentials for a major telephone company, internet company.
[00:20:06] I won't name names here.
[00:20:08] My data was part of that.
[00:20:11] Right after that, I started getting a whole bunch of text messages of,
[00:20:16] Kirsten, would you like to win this gift card?
[00:20:20] Click here now while it's still available.
[00:20:23] No, no, no, no.
[00:20:23] Don't click.
[00:20:24] Just delete.
[00:20:25] Right.
[00:20:26] And that could be also something, especially for a poll worker, right?
[00:20:32] Poll workers will have access, depending upon the state.
[00:20:36] Again, you'll have your own phone, which may or may not be allowed when you're working there.
[00:20:41] Again, it varies by state.
[00:20:42] And I'm not an expert on every state.
[00:20:45] So I've always said, hey, in the guidance we've said, please be mindful of what your state laws are with regards to being a poll worker or a poll watcher.
[00:20:52] But the poll worker themselves might be able to have access right there to their phone, number one.
[00:20:59] Number two, they might actually be working on a laptop where they're checking in voters.
[00:21:05] And there could be a pop-up screen that comes up.
[00:21:08] Don't click those links and report that a link came up.
[00:21:12] Report that there was a pop-up.
[00:21:13] Because you don't know if that is something where a threat actor is trying to get your attention, get a click, and deposit something on the laptop, deposit something on your cell phone, right?
[00:21:26] That's really good that you've got this guide.
[00:21:28] And that it's bringing these kind of issues to people's attention.
[00:21:33] And I think it is so important because a lot of the people who are the election officials, the poll workers, the people who work the local precincts, they're usually not always, but they're normally a little bit older.
[00:21:47] And they may not be quite as tech-savvy.
[00:21:51] They may be, and I'm not saying that people who are older are not as tech-savvy, but they just may not be as up on what are cybersecurity best practices.
[00:22:02] And so it's a good way to just explain it to them in everyday English.
[00:22:06] Yeah, that's right.
[00:22:07] And we love our poll workers and poll watchers.
[00:22:10] I just think it's so fabulous to volunteer in civic society for something so important as our election.
[00:22:16] So I love that.
[00:22:17] And this really has been a labor of love for many of us in the cybersecurity industry who have been involved in this.
[00:22:23] We want to empower and equip these individuals with just some good sense, good common sense language, and good common sense guidance around what could go wrong and why.
[00:22:35] Because they're not everyday involved in what we're involved in.
[00:22:40] And I think that there is also a presumption.
[00:22:44] I've been a poll worker, right?
[00:22:46] And I've been an observer.
[00:22:48] I've been on both sides.
[00:22:49] There's a presumption that what's standing in front of you is secure because you don't think that it wouldn't be.
[00:22:56] Why would you think that there would be a problem?
[00:22:58] You're taught the process of the elections.
[00:23:01] You're taught how to process through, check a voter in, get them their ballot, instruct them how to use the voting machine, instruct them, look at your ballot, then put it in the tabulator.
[00:23:13] Everyone is instructed on that process.
[00:23:15] And that belies the presumption that every step of the way is secure because it's never brought to their attention that it might not be.
[00:23:27] Right?
[00:23:28] And I'm not saying that they're not.
[00:23:30] But, you know, I will say this.
[00:23:32] In my experience in corporate, big corporate, we never say something is 100% secure.
[00:23:39] We never say that.
[00:23:41] You know why?
[00:23:42] It's not.
[00:23:43] Right.
[00:23:44] Unless it's completely offline and it's paper and pencil or paper and pen and it's that one piece of paper.
[00:23:51] In our digitally connected world, everything is accessible.
[00:23:56] It's a double-edged sword.
[00:23:58] It's a beautiful thing.
[00:23:59] We can build education for the world over.
[00:24:02] We can do healthcare by Zoom in a lot of ways.
[00:24:06] But the double-edged sword of that is that it's accessible.
[00:24:10] Because it's accessible, it's accessible to threat actors, right?
[00:24:15] Right.
[00:24:15] Yeah.
[00:24:15] So, working on the nonprofit with you, you had other cybersecurity experts working with you?
[00:24:22] Yes.
[00:24:23] Yes, I do.
[00:24:23] What kind of backgrounds did they have?
[00:24:24] All Fortune 500.
[00:24:26] Either current chief information security officers or former chief information security officers.
[00:24:31] I've got a couple of people who run IT before.
[00:24:34] I have some corporate security officers who have run what you talked about in the paper mill, the OT side, operational technology and manufacturing.
[00:24:43] I've done that as well from the cybersecurity side of operational technology.
[00:24:47] And three of the companies, actually, that I've had the privilege to serve have also been responsible for the security of the manufacturing floor, things like that.
[00:24:58] So, we're actually adding more people to the council as well.
[00:25:01] I've had some people come out of the woodwork.
[00:25:03] They're going, oh, we want to be involved.
[00:25:04] How do I?
[00:25:05] That's amazing.
[00:25:06] Yeah.
[00:25:06] That's really exciting.
[00:25:07] It is.
[00:25:07] It's very exciting.
[00:25:08] I think the community wants to give back.
[00:25:10] The cybersecurity community loves to give back.
[00:25:12] Now, are you looking at any other projects on the horizon?
[00:25:16] We are.
[00:25:17] And one of my passion projects that I actually started a few months ago, and then this one took precedence, of course, because of the timing on it.
[00:25:26] I'm very passionate about anti-human trafficking.
[00:25:30] Oh.
[00:25:30] Very passionate about this.
[00:25:32] I've been involved with A21, which is the Initiative to Abolish Human Trafficking in the 21st Century, and many others as well.
[00:25:40] Now, I've been very passionate about this.
[00:25:43] And one of the things that I recognized, and that many have recognized, it's not just me, is that our youth of today are being targeted.
[00:25:51] They're being targeted online.
[00:25:54] Youth in America, we'll just talk about America.
[00:26:08] And kids these days do not understand, because their brains are not fully formed yet, and they're beautiful, and they're so impressionable, and they're learning, and they're growing.
[00:26:16] They don't realize that everyone who presents themselves online isn't necessarily who they say they are.
[00:26:24] And so what we've seen, and there's studies out there, and there's reports out there, where children are being directly targeted by pedophiles for grooming and for trafficking.
[00:26:38] Trafficking can be, by the way, physical movement of a human being away from where they agree to be located, physically, humanly, geolocation-wise.
[00:26:51] It can also be images, and the images are then moved.
[00:26:55] The videos are then moved, sold, licensed, whatever these things are.
[00:27:00] That is also human trafficking.
[00:27:02] And so what I've been working on in the background a bit, and this is going to be the next passion project for our institute, is working on digestible, exciting content for today's youth using social media to help them understand the perils that are there in a way that they want to see it.
[00:27:24] I mean, it's great.
[00:27:25] It's great.
[00:27:26] There's some states, Florida included, where they've mandated some education for K-12, which is a course kind of like taking sex ed or taking English, that kind of a thing, just to help kids understand what it looks like.
[00:27:40] I don't know about you, but when I was in school, I didn't want to be forced to watch anything.
[00:27:44] I didn't like that at all.
[00:27:46] But I really feel passionately that we can reach today's youth on the social media platforms that they are on.
[00:27:52] And so I'm actually working with a couple of those social media platforms who are also equally passionate about this and seeing what is the art of the possible.
[00:28:03] What might we be able to do next?
[00:28:06] That is amazing and so very important.
[00:28:11] I think what happens online with kids and youth today, it is alarming.
[00:28:17] It is.
[00:28:17] And I don't think that the kids understand it.
[00:28:23] And I don't think that their parents completely understand it.
[00:28:26] And that creates a huge section of society that is extremely vulnerable to predators.
[00:28:35] There's a reason why chief information security officers don't let their kids have cell phones until a particular age.
[00:28:43] Don't let them have access to social media unless they're monitoring the social media traffic.
[00:28:51] There's a reason for that.
[00:28:52] There's a reason why chief information security officers actually don't have social media platforms either.
[00:28:56] They're not on it themselves.
[00:28:58] And it's because of this very threat.
[00:29:02] Threat actors come in all shapes and sizes.
[00:29:05] They come from all over the world, including domestically in the United States of America, unfortunately.
[00:29:10] And they're targeting.
[00:29:12] They are opportunistic.
[00:29:14] And they target what they aim to exploit, whether that's financially or it's humans or it's the thinking.
[00:29:22] It's all of these things, right?
[00:29:24] And so I'm really excited about that particular thing, initiative.
[00:29:30] I've been known for taking on very, very large chunks and aggressive chunks of we need to solve this problem.
[00:29:37] But it's true.
[00:29:37] We need to support our kids these days.
[00:29:41] We do.
[00:29:42] With just good knowledge.
[00:29:44] And we need to support their parents with good knowledge.
[00:29:46] Because, I mean, when my parents told me to not do something, I found a way to do it anyway.
[00:29:50] Guilty.
[00:29:51] That's me.
[00:29:51] I did that.
[00:29:52] But I think if we can target both then, if we can really give good digestible information into the hands of parents, single parents, you know, grandparents, aunties and uncles, cousins, people who are helping raise, even teachers who are helping raise today's youth.
[00:30:08] And get it into the hands of the youth in a way that they'll, like, want to watch it.
[00:30:13] We're still working on that part.
[00:30:14] Because I feel like we do need to do a social media campaign with that age group, using that age group, with people who can actually, I don't know, can you envision a dance?
[00:30:25] Can we have a song or a dance?
[00:30:26] Can we talk about cybersecurity?
[00:30:27] I'm not sure.
[00:30:28] That may be a little bit too much to ask.
[00:30:29] But I think the vision of this is right.
[00:30:34] And all of the people that I talk to about this, whether they're parents and in cyber or cyber without kids or just parents in general,
[00:30:42] they're like, yes, we need this.
[00:30:45] And security for our kids is not a partisan topic.
[00:30:52] Well, it shouldn't be.
[00:30:54] It should not be.
[00:30:54] I haven't encountered a situation.
[00:30:57] There are a few where I'm like, wait, this shouldn't be partisan.
[00:31:00] But I know what I'm talking to every day.
[00:31:03] Yeah.
[00:31:03] Americans think that when it comes to our kids, we should be protecting kids.
[00:31:06] That's right.
[00:31:07] That's right.
[00:31:07] Save our children.
[00:31:08] Right.
[00:31:08] Absolutely.
[00:31:09] Yeah.
[00:31:09] So there are, of course, differences in approaches.
[00:31:13] In the how.
[00:31:14] I think.
[00:31:15] Yeah, in the how.
[00:31:16] And I think, you know, this also, Jenny Beth, is one of the reasons why I really wanted to get this institute off the ground.
[00:31:26] There are some things in life that are not partisan.
[00:31:30] Cybersecurity is not a partisan issue.
[00:31:32] It's whether it's secure or not secure.
[00:31:35] And I would even say there is no such thing as secure.
[00:31:38] We risk reduce.
[00:31:39] We risk manage.
[00:31:40] That's what we do in cybersecurity.
[00:31:42] We never come out with a report that says, oh, this thing is 100% secure.
[00:31:46] Because it's not physically or digitally possible to make that make sense or to make that work out.
[00:31:53] The institute is strictly nonpartisan.
[00:31:58] And if you look at my tech advisory council, we come from all walks of life, from different backgrounds, different religious beliefs, different political belief systems.
[00:32:09] Because cybersecurity is not a political topic.
[00:32:14] Saving our youth is not a political topic.
[00:32:17] You know, I just, I'm very passionate about that.
[00:32:20] Of course, we all have our own opinions.
[00:32:22] We all do have our own opinions as individuals.
[00:32:25] But the institute itself is here to establish and to advocate for strong cybersecurity for citizens around the world, starting right here in America.
[00:32:35] Very good.
[00:32:36] It's great.
[00:32:37] So where can people go to find out more information and to find the handbooks you've created for the election officials and poll workers and also for the observers and poll watchers?
[00:32:48] Absolutely.
[00:32:49] We have a website set up.
[00:32:50] It is instituteforcybercivics.org.
[00:32:56] Instituteforcybercivics.org.
[00:32:58] And we're also on every social media platform at instituteforcybercivics.
[00:33:05] So institute for with the number four.
[00:33:07] With the number four on social media platforms, but the spelled out four on our website.
[00:33:14] On the website.
[00:33:14] Yeah, absolutely.
[00:33:15] Well, very good.
[00:33:16] Thank you so much for joining me today, Kirsten.
[00:33:19] Thank you.
[00:33:19] It's been a pleasure talking with you.
[00:33:20] Thanks for having me.
[00:33:21] The Jenny Beth Show is hosted by Jenny Beth Martin, produced by Kevin Mooneyham, and directed by Luke Livingston.
[00:33:30] The Jenny Beth Show is a production of Tea Party Patriots Action.
[00:33:35] For more information, visit teapartypatriots.org.
[00:33:41] If you liked this episode, let me know by hitting the like button or leaving a comment or a five-star review.
[00:33:47] And if you want to be the first to know every time we drop a new episode, be sure to subscribe and turn on notifications for whichever platform you're listening on.
[00:33:56] If you do these simple things, it will help the podcast grow, and I'd really appreciate it.
[00:34:02] Thank you so much.